Solutions
Solutions
Product
Product
Services
Services
Sign In
As organizations continue to reinvent their digital leadership strategy, our security program ensures that change, transformation, and continuous innovation is implemented securely.






We design, build, and implement cybersecurity solutions that are tailored to your needs.

Utilize our deep pool of cybersecurity engineering resources to accomplish your business objectives.

Enlist our certified experts to assess the cybersecurity risk to your business against leading security frameworks.

Enhance your cybersecurity posture with our 24x7 Managed Security Services.
A Rapid Risk Assessment utilizing a leading security framework to provide you with prioritized recommendations to immediately improve your business' cyber risk posture.
A prioritized security roadmap with cost estimates and level of effort required to address your most critical areas of cyber risk and rapidly improve your cybersecurity program.
A modern Zero-Trust cybersecurity architecture that is designed to proactively defend against advanced cyber threats targeting your business.
Implement Defense in Depth cybersecurity technologies and controls that scale with your business.
Managed Security Services to proactively monitor, detect, and respond to cyber threats.
Accelerate the modernization of cybersecurity for your business
Our recommendations are thoroughly vetted to ensure they achieve your desired outcomes, while seamlessly integrating with existing infrastructure and applications.

Focused cybersecurity solutions that help you scale your business while adhering to applicable industry standards and regulatory requirements.

Leverage cost-effective and predictable subscription models to implement a cybersecurity program that scales with your business.

On-demand expertise
Immediately augment your cybersecurity program with our global team of trained and certified cybersecurity professionals.
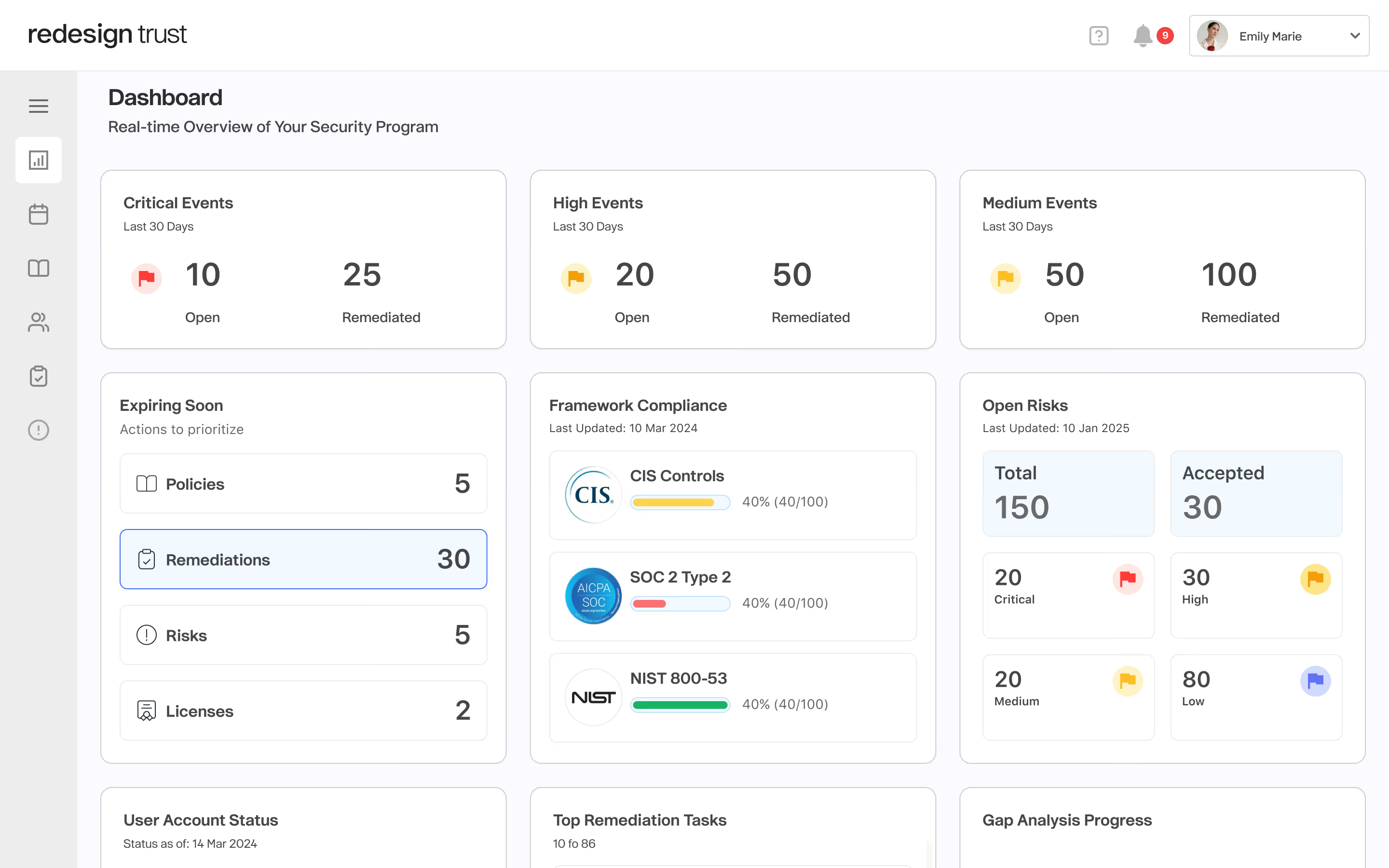
A real-time cybersecurity dashboard to effectively manage your cybersecurity program and automate your compliance requirements.
Real-Time Security Oversight
Monitor and manage cybersecurity with a live dashboard, automating compliance and risk tracking.
Streamline adherence to 80+ frameworks with automated evidence collection and reporting.
Scalable Expert Support
Get a dedicated coordinator and global specialists for tailored, cost-effective security solutions. Explore the Trust Portal

Reconnect interdependencies within the organization
Redesign helps you reduce downtime, maximize efficiency, and empower your teams to focus on strategic priorities—not routine tasks.